Current Threat Level
Check the current security threat level according to Symantec
Suspicious Email?
Have you received an email that you are suspicious of? Here's some warning signs of scam emails.
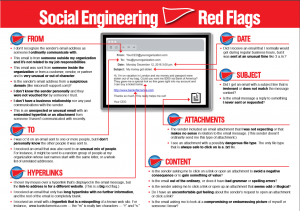
Check the message details: Is the message from someone you know? Is it sent directly to you or to a group of people. Does the subject of the email make sense for something you would receive? And was the message sent at a strange time?
Check the contents of the message: Does the message make sense for something you would normally receive? Is the spelling and grammar a mess?
Links in the message: Hover your mouse over the link, does the tooltip say the same address that the text does? If the link is shortened like bit.ly, tinyurl.com or goo.gl try copying it into this tool, does it go to a site you know of?
Attachments: Were you expecting an attachment from this person? Does it make sense to have an attachment with this message? Is the attachment file type actually a document (Word, Excel, PowerPoint, etc) or something else (EXE, VBS, etc)?
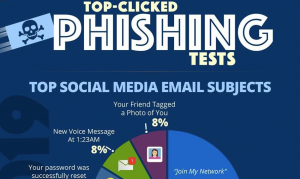
Click the images below for examples of what to look for & what are the most used phishing subject matters
If you still aren't sure about a message you can forward it on to ALES IT and we can take a look at it for you.
Tips for Protecting Yourself
- Be suspicious of any unsolicited emails, even if from people you know.
- Find out where links go by hovering over them to get the real address and make sure it matches what it claims to be.
- Use a url expander like http://www.getlinkinfo.com/ if the url is shortened (i.e. tinyurl.com or bit.ly), this will let you see exactly where you will end up.
- Check the address bar. If you find yourself on a site that requires entering credentials, always check the address bar to ensure it is the correct site and not a spoof.
- If you are logging into a site check that it is an encrypted connection by looking for the lock icon in the address bar.
- If, by mistake, you clicked on a link or a file, do not delete the email, inform ALES IT about it first.
- Be wary of social engineering, where someone attempts to gain information from you through manipulation. If someone calls or emails you asking for sensitive information, it’s okay to say no. You can always call the company directly to verify credentials before giving out any information.
- Never share your password with anyone. Neither ALES IT or IST will ask you directly for it either.